In today's highly interconnected digital landscape, Secure Shell (SSH) stands as a cornerstone for securing communications within IoT networks on Windows systems. As the Internet of Things (IoT) continues to expand at an unprecedented rate, ensuring secure and reliable communication between devices has never been more critical. SSH provides cutting-edge encryption and authentication mechanisms, effectively safeguarding data transmission against unauthorized access and sophisticated cyber threats.
SSH has emerged as an indispensable tool for network administrators and developers committed to protecting sensitive data. It enables secure access to remote systems, empowering users to manage IoT devices efficiently without compromising security. This comprehensive guide will delve into the intricacies of SSH, focusing on its role and implementation within IoT networks operating on Windows platforms.
By gaining a deeper understanding of SSH principles and its practical application, you can significantly enhance the security of your connected devices. Whether you're a beginner or an experienced professional, this resource will equip you with the knowledge needed to harness SSH effectively in your IoT environment.
Read also:Woo Do Hwan The Inspiring Journey Of A Rising Star
Table of Contents
- Introduction to Secure Shell (SSH)
- SSH in IoT Networks
- Windows Implementation of SSH
- Benefits of Using SSH
- Security Features of SSH
- Common Attacks in IoT Networks
- Best Practices for SSH in IoT
- Troubleshooting SSH Issues
- Integration with Windows
- Future Trends in SSH and IoT
Understanding Secure Shell (SSH)
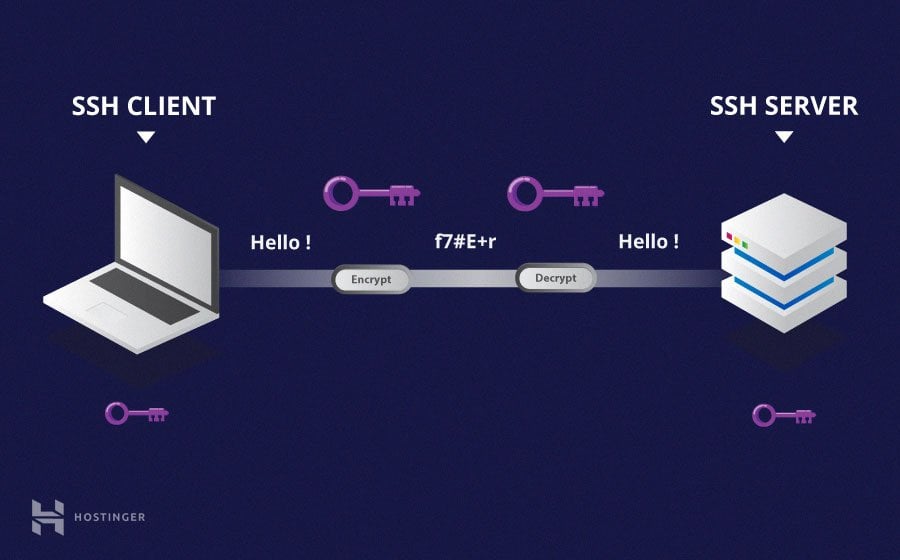
Secure Shell (SSH) is a robust cryptographic protocol designed to secure communication over untrusted networks. It establishes a secure channel for data exchange between a client and server, ensuring confidentiality, integrity, and authentication. Originally developed in 1995 by Tatu Ylönen, SSH has since evolved into a globally recognized standard for secure remote access.
Core Features of SSH
- Encryption: SSH encrypts all data transmitted between the client and server, providing robust protection against eavesdropping and interception.
- Authentication: It supports a variety of authentication methods, including passwords, public key authentication, and certificates, ensuring secure access control.
- Integrity: SSH employs cryptographic hash functions to verify that data remains unaltered during transmission, enhancing data reliability.
SSH has become a vital component in modern networking environments, particularly in IoT ecosystems where security is of paramount importance. Grasping its fundamental functionalities is essential for its effective implementation in IoT networks on Windows systems.
The Role of SSH in IoT Networks
IoT networks comprise a vast array of interconnected devices that communicate with one another and with centralized servers. These devices often operate in environments where security risks are significant, making SSH an invaluable solution for securing their communications.
Why SSH is Essential for IoT
- Secure Remote Access: SSH enables administrators to remotely manage IoT devices without exposing them to unauthorized access, streamlining operations and maintenance.
- Data Protection: By encrypting data transmissions, SSH ensures that sensitive information remains confidential, mitigating the risk of data breaches.
- Scalability: SSH is capable of handling large-scale IoT deployments, supporting secure communication across thousands of devices, making it ideal for enterprise-level applications.
Integrating SSH into IoT networks on Windows involves configuring both the client and server components to ensure seamless and secure communication. This section will explore the necessary steps to achieve this integration effectively.
Implementing SSH on Windows
Windows has fully embraced SSH, offering native support for both client and server functionalities since Windows 10 and Windows Server 2019. This integration simplifies the setup process for SSH in IoT devices running on Windows platforms, enhancing their security capabilities.
Enabling SSH on Windows
- Install Features: Install the OpenSSH Client and Server features via the Windows Features menu to enable SSH functionality.
- Configure Settings: Customize the SSH server settings in the sshd_config file to align with your specific requirements and enhance security.
- Set Firewall Rules: Establish firewall rules to allow SSH traffic on the designated port (default is 22), ensuring smooth communication while maintaining security.
Once properly configured, Windows-based IoT devices can leverage SSH for secure communications, significantly improving their overall security posture.
Read also:Vegamoviesarchive Your Ultimate Destination For Movie Downloads
Advantages of SSH in IoT Networks
Adopting SSH in IoT networks on Windows offers numerous advantages, contributing to a more secure and efficient operational environment:
- Enhanced Security: SSH provides advanced encryption and authentication mechanisms, effectively safeguarding data from a wide range of cyber threats.
- Reliability: It ensures reliable data transmission even under challenging network conditions, maintaining connectivity and performance.
- Flexibility: SSH supports various authentication methods, empowering organizations to select the most appropriate option based on their unique needs.
- Cost-Effectiveness: As an open standard, SSH eliminates the need for proprietary solutions, reducing costs while maintaining high security standards.
These benefits make SSH an attractive and practical choice for securing IoT networks on Windows systems.
Advanced Security Features of SSH
SSH incorporates several state-of-the-art security features that make it a preferred choice for securing IoT communications:
- Public Key Cryptography: SSH utilizes public key infrastructure (PKI) to authenticate users and devices, ensuring secure access and preventing unauthorized entry.
- Encryption Protocols: It supports modern encryption algorithms like AES and ChaCha20, providing robust data protection against sophisticated cyber threats.
- Message Authentication Codes (MAC): SSH employs MACs to verify the integrity of transmitted data, ensuring that information remains unaltered during transmission.
By leveraging these advanced security features, organizations can establish secure connections within their IoT networks, minimizing the risk of data breaches and ensuring the protection of sensitive information.
Addressing Common Attacks in IoT Networks
IoT networks are vulnerable to various cyberattacks, many of which can be effectively mitigated through the proper implementation of SSH:
- Man-in-the-Middle (MitM) Attacks: SSH's encryption and authentication mechanisms prevent attackers from intercepting and altering communications, ensuring data integrity.
- Brute Force Attacks: Implementing public key authentication significantly reduces the risk of brute force attempts to guess passwords, enhancing security.
- Denial of Service (DoS) Attacks: Configuring SSH server settings can help mitigate DoS attacks by limiting connection attempts and enforcing strict access controls.
Understanding these potential threats and how SSH addresses them is crucial for maintaining the security of IoT networks on Windows systems.
Optimizing SSH Security in IoT
To maximize the security benefits of SSH in IoT networks on Windows, consider adopting the following best practices:
- Use Strong Authentication Methods: Prioritize public key authentication over password-based methods to enhance security and reduce the risk of unauthorized access.
- Regularly Update SSH Software: Keep the SSH client and server software up to date to protect against known vulnerabilities and ensure compatibility with the latest security standards.
- Limit Access: Restrict SSH access to authorized users and devices only, utilizing firewalls and access control lists to enforce strict security policies.
Implementing these best practices ensures that your IoT network remains secure and resilient against potential threats, safeguarding your devices and data.
Resolving Common SSH Issues
Although SSH is a robust and reliable protocol, it can occasionally encounter issues that require troubleshooting. Common problems include connection failures, authentication errors, and performance bottlenecks.
Steps to Resolve SSH Issues
- Check Server Logs: Examine SSH server logs for error messages that can provide valuable insights into the problem and guide the troubleshooting process.
- Verify Service Status: Confirm that the SSH service is running and listening on the correct port to ensure proper functionality and connectivity.
- Review Firewall Rules: Ensure that firewall rules allow SSH traffic and that no conflicting network configurations exist, maintaining seamless communication.
By following these systematic steps, you can efficiently identify and resolve SSH-related issues in your IoT network, ensuring optimal performance and security.
Seamless Integration of SSH with Windows
Integrating SSH with Windows-based IoT devices involves configuring both the operating system and the SSH service to work harmoniously together, ensuring secure and efficient communication:
Key Considerations for Integration
- Native Support: Ensure that the Windows operating system supports SSH natively or through reliable third-party tools, facilitating seamless integration.
- Permission Configuration: Configure user permissions and access controls to align with organizational security policies, maintaining a secure operational environment.
- Thorough Testing: Conduct comprehensive testing of the SSH connection to confirm that it functions as expected within the IoT environment, identifying and addressing any issues proactively.
This integration process is vital for realizing the full potential of SSH in securing IoT networks on Windows, enhancing both security and operational efficiency.
Emerging Trends in SSH and IoT
As IoT continues to evolve, the role of SSH in securing network communications is likely to expand, driven by emerging trends and technological advancements:
- Quantum-Resistant Cryptography: With the advent of quantum computing, SSH may incorporate quantum-resistant algorithms to maintain its security and effectiveness in the face of new challenges.
- AI-Driven Security: Artificial intelligence could revolutionize SSH's ability to detect and respond to security threats in real time, enhancing its proactive defense capabilities.
- Cloud Integration: SSH is expected to play a pivotal role in securing cloud-based IoT solutions, facilitating secure communication between devices and cloud services while maintaining high performance and reliability.
Staying informed about these emerging trends will enable organizations to prepare for the future of IoT security, ensuring that their networks remain protected and resilient against evolving threats.
Conclusion
In summary, understanding and leveraging Secure Shell (SSH) in IoT networks on Windows is essential for maintaining robust security in an increasingly interconnected world. By utilizing SSH's advanced encryption, authentication, and integrity features, organizations can effectively protect their IoT devices and data from a wide range of cyber threats.
We encourage readers to implement the best practices outlined in this guide and to stay updated on the latest developments in SSH and IoT security. Your feedback and experiences are valuable, so feel free to share them in the comments below. Additionally, explore other articles on our site for further insights into cybersecurity and IoT technologies, empowering you to safeguard your digital ecosystem effectively.